How Secure Are
you?
Are you confident enough in the state of your technology security, threat identification and prevention status not to worry about a breach, ransomware or cyberattack?
You simply cannot establish a value for your data – but you can take measures to protect yourself from risk.
Our clients turn to our managed security services to identify and shore up weaknesses, gain security expertise and train their staff to improve security awareness, preventing intrusion.
Possibilities
- Secure your business, employee and customer data
- Monitor for and Identify potential threats before they escalate
- Benefit from ongoing penetration and vulnerability testing to ensure maximum security
- Sleep better at night knowing your business is secure
Continuous Security Oversight
Our managed security services offer continuous oversight, 24/7/365. Attempting to handle your critical security needs yourself requires a large investment in money, manpower and security expertise.
We conduct regular vulnerability and penetration testing, perform security scans routinely, and take care of other security management functions for your organization, as well as deliver security awareness training to you and your staff, your biggest security vulnerability.
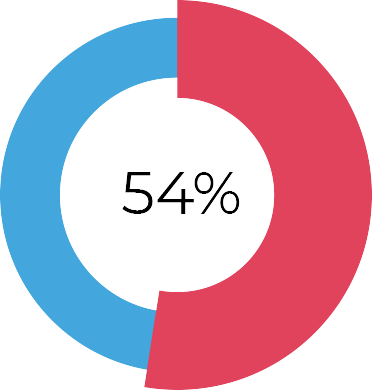
Number of organizations that experienced one or more ransomware incidents in 2017
How it Works
We’ll conduct a discovery meeting to understand your particular business security requirements and concerns. We’ll next schedule a technical specialist to visit your location(s) and conduct a security assessment and conduct scans and penetration testing with our non-invasive tools and processes to identify internal and external vulnerabilities that should be addressed; and data that should be encrypted.
We’ll also identify if any of your business data, email accounts or passwords have been compromised and are available on the Dark Web.
Once we’ve collected this threat intelligence, we’ll analyze it to develop a strategy to harden and secure your infrastructure, devices, platforms and services from external attack, and coninually monitor your systems for rapid threat detection. From there, we’ll put together an ongoing security awareness training and testing program to educate your staff in ways to identify and avoid electronic and socially-engineered security threats.
-
Discovery
Meeting -
Security
Assessment -
Analysis &
Remediation Plan
Pain Points Solved
- Protect Against Electronic Security Risks Secure your infrastructure, devices, platforms and services against security threats
- Meet Regulatory Compliance Standards Achieve regulatory and industry security compliance with hardened security
- Increase Staff Security Awareness Employees are the weakest link in your business security, ongoing security awareness training and testing will strengthen your defenses
- Increase Productivity and Innovation A strong security posture increases business productivity and accelerates innovation
Productivity levels in the workplace can peak when social media is restricted on the corporate network.”
Implementation Timeline
Once we’ve agreed to engage, a security discovery meeting can be scheduled within 2 weeks. Following our discovery meeting, we’ll be able to schedule an onsite security assessment within the following week. For a typical small office location, our onsite security assessments can usually be completed in 2 days.
It will take us approximately a week to analyze the information gathered during the discovery meeting and the technology assessment. We’ll be able to meet with you the following week to deliver our findings and recommendations.
-
Discovery Meeting
Week 1
-
Security Assessment
Week 2
-
Analysis & Remediation Plan
Week 3
White Paper
Our Benefits of Managed Security Services whitepaper explores the many advantages of engaging with an enterprise-level technology firm to address your managed security needs.
- What is Cyber Security?
- Threat to Small and Medium Business?
- What You Need to Know About Ransomware, Business Email Compromise and The Dark Web
- Why Your Employees May Be Your Biggest Threat
- How to Protect Your Business